Linux Hands on
Kali/ Raspberry pi/ Pihole+Unbound/ OMV/Docker/ Portainer - Notes
DISCLAIMER:
- This document contains unedited notes and has not been formally proofread.
- The information provided in this document is intended to provide a basic understanding of certain technologies.
- Please exercise caution when visiting or downloading from websites mentioned in this document and verify the safety of the website and software.
- Some websites and software may be flagged as malware by antivirus programs.
- The document is not intended to be a comprehensive guide and should not be relied upon as the sole source of information.
- The document is not a substitute for professional advice or expert analysis and should not be used as such.
- The document does not constitute an endorsement or recommendation of any particular technology, product, or service.
- The reader assumes all responsibility for their use of the information contained in this document and any consequences that may arise.
- The author disclaim any liability for any damages or losses that may result from the use of this document or the information contained therein.
- The author reserve the right to update or change the information contained in this document at any time without prior notice.
- Any attempts to perform penetration testing or ethical hacking on systems or networks should be done with the explicit permission of the system/network owner. Unauthorized access is illegal and can result in serious legal consequences.
- It is important to fully understand the scope of the testing and to only test within that scope. Testing outside the agreed upon scope is considered unauthorized and may result in legal action.
- Any findings or vulnerabilities discovered during testing should be reported to the system/network owner immediately and kept confidential until a fix can be implemented.
- It is recommended to use a separate, dedicated testing environment rather than testing on a live production system to minimize the risk of accidentally causing damage or downtime.
- It is important to take steps to protect your own identity and prevent accidental data leaks or exposure of sensitive information during testing.
- It is also recommended to follow a standard code of ethics for ethical hacking and penetration testing.
REFERENCES:
- https://www.kali.org/tools/
- https://www.gnu.org/software/grub/manual/grub/html_node/Command_002dline-and-menu-entry-commands.html
- https://developer-old.gnome.org/NetworkManager/stable/nmcli.html
- https://forum.greenbone.net/
- https://docs.pi-hole.net/guides/dns/unbound/
- https://www.youtube.com/@KMDTech
This blog article covers:
- Kali Linux tools:
- It explores the various tools available in Kali Linux, a popular operating system used for cybersecurity and penetration testing.
- Dual booting Kali Linux with Windows:
- It provides a guide on how to install and set up Kali Linux alongside Windows, allowing users to choose between the two operating systems during startup.
- Building a NAS using Raspberry OS Lite:
- It explains the process of creating a Network Attached Storage (NAS) system using Raspberry Pi with the lightweight Raspberry OS Lite operating system.
- Pihole + unbound
- It explains how you can set up network-wide ad blocking using your own Linux hardware. The Pi-hole is a DNS sinkhole that helps protect your devices from unwanted content, all without the need to install any software on individual devices.
- VNC Virtual mode Along with OMV
- These steps enable you to install a basic virtual desktop environment on a headless Raspberry Pi Lite with OpenMediaVault. This allows you to access the desktop using a VNC viewer.
Contents:
- upgrade commands
- DUAL Boot Kali Linux with Windows
- GVM
- Nessus
- WiFi
- GREP command
- Configuring VPN
- Scanning networks on monitor mode
- Configuring NAS (Network Attached Storage) on Raspberry Pi
- Install OMV - openMediaVault
- Install Plex
- Setting Up NordVPN
- Enable Firewall on NAS
- Installing Pihole
- How to Change DNS in Kali Linux
- Setting up VNC Server with OMV on Raspberry Pi Lite (Headless)
- How to connect from Kali to Raspberry- Pi using VNC-viewer
Update the kali with complete Distribution upgrade:
- sudo apt update
- sudo apt upgrade
- sudo apt full-upgrade -y
- sudo apt dist-upgrade -y
How to Get Hostname and version of linux
- hostnamectl
- lsb_release -a
- cat /etc/os-release
- external ip address
- $ curl ifconfig.me
Search a command to install from CLI:
Kali Linux : Boot loop error
- kali@kali: ls -la
- kali@kali: sudo chown kali:kali .Xauthority
- kali@kali: sudo chown kali:kali .ICEauthority
- kali@kali: reboot
Mount a Network folder on Linux
- Sudo apt install cifs-utils
- sudo mkdir /mnt/nwshare
- sudo mount -t cifs //10.0.0.1/share /mnt/nwshare
- prompt to enter the network password.
**************************************************************
DUAL Boot Kali Linux with Windows
- ┌──(kali㉿kali)-[~]
- └─$ sudo os-prober
/dev/sda1:Windows
Run update-grub
- ┌──(kali㉿kali)-[~]
- └─$ sudo update-grub
Just uncomment the below command
- ┌──(kali㉿kali)-[~]
- └─$ sudo nano /etc/default/grub
#GRUB_DISABLE_OS_PROBER=false
Once again Run update-grub
- ┌──(kali㉿kali)-[~]
- └─$ sudo update-grub
done
└─$ reboot
Windows 11 Update Broke Dual Manager: FIX
Step 1:
Step 2:
Now Mounting the Linux file system partition & EFI boot partition
- :$> mount /dev/sda4 /mnt
- :$> mount /dev/sda1 /mnt/boot/efi
- :$> for i in /dev /dev/pts /proc /sys /run; do mount -B $i /mnt$i; done
- :$> chroot /mnt
- :$>grub-install /dev/sda
- grub-install: waring EFi variables cannot be set on this system
Mounting the EFI parameters
- :$>mount -t efivarfs none /sys/firmware/efi/efivars
- :$>grub-install /dev/sda
- :$>update-grub
Verifying the boot file list
- :$>efibootmgr
- :$>exit
- :$>reboot
**************************************************************
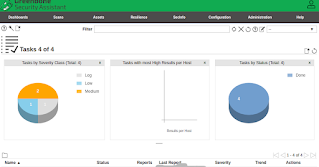
GVM: Greenbone Vulnerability Manager
- ┌──(kali㉿kali)-[~]
- └─$ sudo apt install gvm
- ┌──(kali㉿kali)-[~]
- └─$ sudo gvm-setup
[+] Done
[*] Please note the password for the admin user
[*] User created with password '**********************.
[>] You can now run gvm-check-setup to make sure everything is correctly configured
- ┌──(kali㉿kali)-[~]
- └─$ sudo gvm-check-setup
It seems like your GVM-22.4.1 installation is OK.
- ┌──(kali㉿kali)-[~]
- └─$ ss -lnt4
- └─$ sudo gvm-start
[>] Please wait for the GVM services to start.
[>] You might need to refresh your browser once it opens.
[>] Web UI (Greenbone Security Assistant):
https://127.0.0.1:9392
ob for gvmd.service failed because a timeout was exceeded.
See "systemctl status gvmd.service" and "journalctl -xeu
gvmd.service" for details.
- sudo nano /etc/postgresql/17/main/postgresql.conf
- edit the port number to reflect 5432
How to change Admin password in GVM:
How to Update GVM feed
Verify GVM certificates
|
| GVM dashboard |
GVM PostgreSQL Collation Error:
Nessus
To access detailed information, refer to the topic "Scanning with Nessus" within the Pentesting- Hands-on article.
- ┌──(kali㉿kali)-[~]
- └─$ sudo dpkg -i Nessus-10.5.1-debian10_amd64.deb
- Then go to https://kali:8834/ to configure your scanner
Testing/ ***************
- ┌──(kali㉿kali)-[~]
- └─$ /bin/systemctl start nessusd.service
**************************************************************
WiFi
┌──(kali㉿kali)-[~]
└─$ nmcli device wifi list
**************************************************************
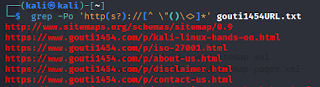
GREP command
- -f is the field like 2nd string or 11th string and
- -d is the delimiter
- sort function
- unique strings only
- Host: 192.168.1.1 () Status: Up
- Host: 192.168.1.4 () Status: Up
- Host: 192.168.1.17 () Status: Up
- Host: 192.168.1.20 () Status: Up
- Host: 192.168.1.22 () Status: Up
- Host: 192.168.1.250 () Status: Up
Configuring VPN to remain anonymous while performing Pentesting:
Restarting the network service
Adding open source vpn accounts to kali
Changing MAC address no to get banned, while performing pentest
Scanning networks on monitor mode
Configuring NAS (Network Attached Storage) on Raspberry Pi
- Raspberry Pi Imager-installer:
- OS= Raspberry PI OS LITE
- Storage= select sd card
- Write:
- use setting to add wifi network & Enable SSH
- select Enable SSH then create the user as "pi" & password.
- then
- Click write
- Insert the image written SD card
- Boot rasp-Pi and get he ip address
- PC settings- Apps -> Optional Features -> Add on optional features - search for open ssh client & open SSH server
- from PC terminal type ssh username@10.10.0.1
- ssh pinas@10.10.1.5
- ssh kali@10.10.1.131
- enter the password used while writing the os.
- pi@raspberrypi:~ $
- Now Updating then Upgrading rasp-Pi
- Install OMV - openMediaVault
- sudo wget -O - https://github.com/OpenMediaVault-Plugin-Developers/installScript/raw/master/install | sudo bash
- Need to configure WiFi after installing OMV
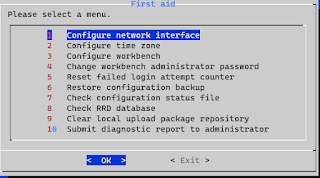
- sudo omv-firstaid
- after installing OVM
- Sudo SU
- omv-firstaid
- Click on Configure Network interface and set up the SSID and Password
|
| omv-firstaid |
- Now log into OMV
- http://10.10.0.1/#/login

|
| Login openMediaVault |
- Change in Default Password
- Storage -> disk

|
|
OMV_Disks |
- Storage -> File System
- Click New -> file system then select the mounted HDD

|
| OMV-file system |
- Storage -> Shared folders
- Click Create ->Shared folder name
- Services
- Enable SMB
- Shares - select the share folder created earlier

|
| Services |
- Same enable for NFS
- Users
- Edit the password for the users
- PC
- Right click and select add network folder

|
| OpenMediaVault Dashboard - desktop |
Remove Shared folders from OMV
- Delete share folders listings
- First deleted the shared folders from Services- SMB, then NFS
- Then, Storage ->shared files
- Next edit the config file to eliminate internal error
- sudo nano /etc/openmediavault/config.xml
- search for mntent and remove the tag <mntent> ... </mntent>
- sudo omv-salt deploy run fstab
- sudo nano /etc/monit/conf.d/openmediavault-filesystem.conf
- clear any identical references to dev-disk-by-label-NAME
- Then reboot
- Now deploy the changes from OMV
Install Plex
- sudo apt install apt-transport-https
- echo deb https://downloads.plex.tv/repo/deb public main | sudo tee /etc/apt/sources.list.d/plexmediaserver.list
- curl https://downloads.plex.tv/plex-keys/PlexSign.key | sudo apt-key add -
- sudo apt update
- sudo apt install plexmediaserver
- sudo systemctl start plexmediaserver
- sudo systemctl enable plexmediaserver
- sudo reboot
- sudo service plexmediaserver status
- 10.10.1.1:32400/web
- Next step is to choose
- Server name
- Add the created shared folders
- network settings
- -> secured connections - preferred
- -> strict TLS configuration
- Access Plex going forward on https://app.plex.tv/desktop/
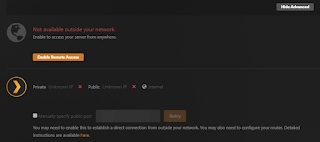
Setting Up NordVPN
- sudo su
- root@pi: sh <(wget -qO - https://downloads.nordcdn.com/apps/linux/install.sh)
- root@pi:nordvpn login --token <paste the token generated from NORDVPN account>
- root@pi: nordvpn set meshnet on
- root@pi: nordvpn meshnet peer list
- To access OpenMediaVault
- Type the meshnet name assigned:
- eg - http://secret.meerkat-alps.nord/
- To access Plex
- eg - http://secret.meerkat-alps.nord:32400/
- To access shared drive directly on android
- File manager -> Network storage -> SMB
- Add manually
- nordVPN- IP-address/Shared-Folder-name
- port 445
- Allowed User Id /Password
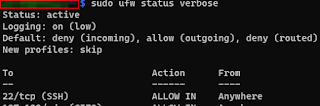
Enable Firewall on NAS
- sudo apt instal ufw
- sudo ufw status verbose
- Status: inactive
- sudo ufw enable
- Command may disrupt existing ssh connections. Proceed with operation (y|n)? y
- Firewall is active and enabled on system startup
- sudo ufw status verbose or
- sudo ufw status numbered
- Status: active
- Logging: on (low)
- Default: deny (incoming), allow (outgoing), disabled (routed)
- sudo ufw disable
- Firewall stopped and disabled on system startup
|
| ufw status verbose |
Can allow to have SSH tunnel connection to the NAS server and Plex server on port 32400. NordVPN is added by default.
- sudo ufw app list
- sudo ufw allow SSH
- sudo ufw allow 32400
- sudo ufw app info SSH
- sudo ufw allow 'www full'
- sudo ufw allow nfs
- sudo lsof -i -P -n
Headless Console Font Size
- sudo dpkg-reconfigure console-setup
- UTF-8
- Guess optimal character set
- Terminal bold
- 16*32 framebuffer only
Installing Pi-Hole
- Installation
- pinas@raspi:~ $ sudo curl -sSL https://install.pi-hole.net | bash
- Change Password for web interface
- pinas@raspi:~ $ pihole -a -p
- raspi:~ $ sudo cat /etc/lighttpd/lighttpd.conf
- server.port = 81
- update the above server port to your choice
- raspi:~ $ sudo cat /etc/lighttpd/external.conf
- if required create and add same server.port =81
- raspi:~ $ sudo systemctl stop systemd-resolved
- raspi:~ $ sudo nano /etc/systemd/resolved.conf
- #Edit the file
- [Resolve]
- DNS=1.1.1.1 # adding values
- FallbackDNS=1.0.0.1# adding values
- #Domains=
- #LLMNR=yes
- #MulticastDNS=yes
- #DNSSEC=allow-downgrade
- #DNSOverTLS=no
- #Cache=yes
- #DNSStubListener=yes
- #ReadEtcHosts=yes
- DNSStubListener=no # To ensure that the system uses the values in this file, you need to add a new line.
- raspi:~ $ sudo ln -sf /run/systemd/resolve/resolv.conf /etc/resolv.conf
Pi-Hole V6 Errors:
- diproton-ads-[^\.]*\.hulu\.com\.akadns\.net
- https://github.com/hagezi/dns-blocklists?tab=readme-ov-file#pro
Pi-hole with Unbound
- pinas@raspi:~ $ sudo apt install unbound
- pinas@raspi:~ $ sudo nano /etc/unbound/unbound.conf.d/pi-hole.conf
- pinas@raspi:~ $ sudo service unbound restart
- pinas@raspi:~ $ dig pi-hole.net @127.0.0.1 -p 5335
- pinas@raspi:~ $ systemctl is-active unbound-resolvconf.service
- active
- pinas@raspi:~ $ sudo cat /etc/unbound/unbound.conf.d/resolvconf_resolvers.conf
- # Generated by resolvconf
-
- forward-zone:
- name: "."
- forward-addr: 10.10.1.1
- forward-addr:
- pinas@raspi:~ $ sudo sed -Ei 's/^unbound_conf=/#unbound_conf=/' /etc/resolvconf.conf
- pinas@raspi:~ $ sudo rm /etc/unbound/unbound.conf.d/resolvconf_resolvers.conf
- pinas@raspi:~ $ sudo service unbound restart
- raspi:~ $ sudo cat /etc/resolv.conf
- update the nameserver to pihole and 1.1.1.1
UFW Firewall Rules:
- "sudo ufw allow 81"
- ufw allow 80/tcp
- ufw allow 53/tcp
- ufw allow 53/udp
- ufw allow 67/tcp
- ufw allow 67/udp
- ufw allow 546:547/udp
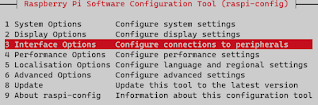
Setting up VNC Server with OMV on Raspberry Pi Lite (Headless)
- pi@raspi: sudo raspi-config
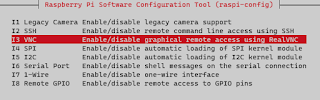
|
| enable VNC |
Installing VNC server and if required vnc viewer
- pi@raspi: sudo apt-get install realvnc-vnc-server
- pi@raspi: sudo apt-get install realvnc-vnc-viewer
- Starting the service
- pi@raspi: sudo systemctl start vncserver-x11-serviced.service
- enabling in boot time
- pi@raspi: sudo systemctl enable vncserver-x11-serviced.service
- pi@raspi: sudo systemctl status vncserver
- if the service doesn't start try to kill any early started services
- kill running process if any.
- pi@raspi: sudo netstat -ptnl | grep vnc
- pi@raspi: sudo kill 986
- pi@raspi: sudo kill 1006
- pi@raspi: sudo systemctl start vncserver
- pi@raspi: sudo systemctl status vncserver.service
- pi@raspi: vncserver
- or vncserver-virtual
- New desktop is raspberryi:1 (10.0.0.1:1)
- pi@raspi: sudo apt-get dist-upgrade
- pi@raspi: sudo apt-get clean
- pi@raspi: sudo apt-get install lxde-core lxappearance
- pi@raspi: sudo apt-get install xterm

|
| VNC viewer |
Vnc Viewer : access denied error
- "Access denied error" occurs, follow below steps,
- pi@raspi: vncserver-virtual
- [Don't use Sudo- root user is not added in "users & permissions" by default under RealVNC server settings]
- pi@raspi: sudo systemctl restart vncserver.service
- pi@raspi: sudo systemctl status vncserver.service
- Option 1
- Raspi username and password
- Option 2
- where authentication is set to VNC password. [refer image - raspi vnc security settings-on]
- no username - the user name is greyed out
- password - use vnc password - changed in the vnc connect window
You can install the Chromium browser on the VNC virtual desktop,

|
| Chromium browser |
The VNC virtual desktop on Raspberry Pi with OpenMediaVault (OMV) has a simple interface. It is crucial to avoid installing lightdm as it will uninstall OMV from your Raspberry Pi and cause it to crash.
- pi@raspi: sudo apt install xserver-xorg-core
- pi@raspi: sudo apt install xserver-xorg-video-fbdev
- pi@raspi: sudo apt install xserver-xorg-input-evdev
- pi@raspi: sudo apt install xinit xfonts-base lxde

|
| Updated icons themes |
Now, you may connect to the Raspberry Pi NAS from an Android device using the NordVPN Meshnet IP address without a computer or monitor.
2025: Setting up VNC Server with OMV on Bookworm- Raspberry Pi Lite (Headless)
- could not connect to vnc server. please ensure that you have the required licence for this feature.
- vnc server cannot currently show the desktop.
sudo raspi-config
- Select the Interface and enable VNC
- Display option -> VNC resolution -> select highest value
Installing Tightvncserver
- sudo apt install lxde-core tightvncserver
- sudo apt-get install xfonts-base
- sudo apt install xserver-xorg-core
- sudo apt install xserver-xorg-video-fbdev
- sudo apt install xserver-xorg-input-evdev
- sudo apt install xinit xfonts-base
- sudo apt install --reinstall lxterminal
- sudo apt install lxpanel
- sudo apt install lxappearance
- sudo apt install -y lxde-core xrdp
How to connect from Kali to Raspberry- Pi using VNC-viewer
no configured security type is supported by 3.3 vnc viewer
- open the VNC Connect window from above virtual desktop,
- Click on the hamburger menu
- Security Tab->
- Encryption = Preferred on
- Authentication = VNC password
- A Pop-up window appears
- Now click Configure to key in new Password
- select the checkbox - Allow connections from legacy VNC viewers.
- password - use vnc password - changed in the vnc connect window
- Connected to RFB server, using protocol version 3.3
- Performing standard VNC authentication
- Password:
- Authentication successful
- Desktop name "****************"
- VNC server default format:
- 32 bits per pixel.
- Least significant byte first in each pixel.
- True colour: max red 255 green 255 blue 255, shift red 16 green 8 blue 0
- Using default colormap which is TrueColor. Pixel format:
- 32 bits per pixel.
- Least significant byte first in each pixel.
- True colour: max red 255 green 255 blue 255, shift red 16 green 8 blue 0
Docker
Portainer:
How to Run Browser in Docker Container
Pi-Alert Using Pi-Hole
Leiweibau/Pi.Alert
- GitHub
- https://github.com/leiweibau/Pi.Alert
- one command Install :
- curl -sSL https://github.com/leiweibau/Pi.Alert/raw/main/install/pialert_install.sh | bash
- Uninstall
- curl -sSL https://github.com/leiweibau/Pi.Alert/raw/main/install/pialert_uninstall.sh | bash
Pucherot/Pi.Alert
- GitHub
- https://github.com/pucherot/Pi.Alert
- one command install:
- curl -sSL https://github.com/pucherot/Pi.Alert/raw/main/install/pialert_install.sh | bash
- Uninstall command:
- curl -sSL https://github.com/pucherot/Pi.Alert/raw/main/install/pialert_uninstall.sh | bash
Jokob-sk/NetAlertX
- GitHub
- https://github.com/jokob-sk/NetAlertX
OMV 7 : OMV-extras
Step 01: Enabling Docker repo
OMV -> System -> Plugins
Step 03: Creating Shared folder structure

|
| share folders added to compose settings |
Step 04: Now Creating Docker Compose File to create containers.
Now need to replace the volume path

|
| Docker Container deployed |
Home Assistant on OMV Container
Install Home Assistant Container
How to Add Tapo Cameras
Raspberry Pi Connect
Jellyfin On Container
- The volume must be mapped correctly to reflect the shared folder created in the NAS. There are two different ways listed to map.
- The volume path can be copied from the absolute path displayed, under OMV-> Storage->Shared Folders
To Access JELLYFIN outside the local network
Self-Signed Certificate
- # openssl req -x509 -newkey rsa:4096 -keyout ./privkey.pem -out cert.pem -days 365 -nodes -subj '/CN=jellyfin.lan'
Verifying - Enter PEM pass phrase:
- openssl pkcs12 -export -out jellyfin.pfx -inkey privkey.pem -in cert.pem -passout pass:
Next step to add SSL certificate path
Next to add the NORDVPN MESHNET IP address
Portainer on OMV
Installing VNC on a Linux Server: Final Working Method After Multiple Attempts
- RealVNC server showing “Missing X server or $DISPLAY”
- Terminal not opening inside VNC
- Display manager not loading correctly
- “Client is not authorized to connect to server & Cannot open display 1.0”
First set of initial view commands to install VNC server to linux server;
- sudo apt install tightvncserver -y
- sudo apt-get install xfce4 lightdm-gtk-greeter dbus-x11 autocutsel -y
- sudo apt install xfce4 xfce4-goodies lightdm -y
Second set of commands to troubleshoot terminal not working in VNC
- sudo apt reinstall xfce4-terminal -y
Third step to reinstall one module at a time and these are optional steps;
- sudo apt reinstall xfce4-settings -y
- sudo apt -y reinstall xfce4-power-manager
- sudo apt -y reinstall xfce4-session
- sudo apt -y reinstall xfce4-notifyd
- sudo apt -y reinstall xfce4-panel
- sudo apt -y reinstall xfce4-whiskermenu-plugin
- sudo apt -y reinstall xfce4-indicator-plugin
- sudo apt -y reinstall xfce4-datetime-plugin
- sudo apt -y reinstall xfwm4-themes
Fourth step Changing display manager:
- sudo apt install slim -y
- sudo apt reinstall lightdm -y
- sudo dpkg-reconfigure lightdm
- # Select: lightdm
- sudo service lightdm start
- $ sudo cat /home/serv4/.vnc/xstartup
- adding the below line to the file;
- startxfce4 &




























Comments
Post a Comment